cryptam office document malware detection and analysis
OVERVIEW
CRYPTAM.COM RANKINGS
Date Range
Date Range
Date Range
CRYPTAM.COM HISTORY
SITE PERIOD OF EXISTANCE
LINKS TO WEB SITE
Wednesday, September 13, 2017. io for RTF zero day CVE-2017-8759. After reading the FireEye blog. We decided to use QuickSand. For the FireEye reported hash fe5c4d6bb78e170abf5cf3741868ea4c.
Malware Tracker provides malware analysis, forensics, and security solutions for enterprise. Use Malware Tracker technology to detect malicious document attachments at the email gateway, and to automate the static analysis of PDF, and common document formats. Home of the free online PDF Examiner. The only web based PDF malware analysis suite and the Cryptam document malware scanner.
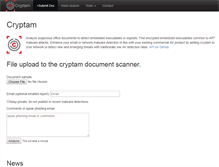
Cryptam is a PHP web application and command line tool to statically analyse streams of office documents for exploits, and uses a cryptanalysis attack to detect and extract embedded executables.
WHAT DOES CRYPTAM.COM LOOK LIKE?


CONTACTS
Fundacion Private Whois
Domain Administrator
Attn: cryptam.com, Aptds. 0850-00056
Panama, Zona 15
PA
Fundacion Private Whois
Domain Administrator
Attn: cryptam.com, Aptds. 0850-00056
Panama, Zona 15
PA
Fundacion Private Whois
Domain Administrator
Attn: cryptam.com, Aptds. 0850-00056
Panama, Zona 15
PA
CRYPTAM.COM HOST
NAME SERVERS
BROWSER ICON

SERVER OS
I discovered that cryptam.com is weilding the Apache/2.4.27 (Amazon) OpenSSL/1.0.2k-fips PHP/5.6.31 os.PAGE TITLE
cryptam office document malware detection and analysisDESCRIPTION
cryptam document malware detection and analysis, ms office, Word, Powerpoit, Excel, RTF, CHM, HLPCONTENT
This site states the following, "Analyze suspicious office documents to detect embedded executables or exploits." We noticed that the web site stated " Find encrypted embedded executables common to APT malware attacks." It also stated " Enhance your email or network malware detection in line with your existing commercial AV product by adding cryptam to your network to detect new and emerging threats with traditionally low AV detection rates. File upload to the cryptam document scanner. Keep private, do not publish in recent malware detections." The header had Malware Tracker Cryptam as the highest ranking keyword.SEEK MORE BUSINESSES
Bypassing certificate checks in OpenSSL 1. Many lines of code have been changed, but most important is a Security Fix that allowed an attacker to bypass certain checks on certificates. The problem is summarized in the changelog of the new release. How does certificate validation work? How does the attack work? Certificate with .
Which is why I decided to write a legacy.
You can use my images, quotes and gifs, but please do not steal and post them as your own. Provide the source, thank you. Florence And The Machine Spectrum. Florence And The Machine Calvin Harris. Is it college yet? Hello Kitty, Goodbye Kitty lol.